Often times you may find that you need to block web messengers due to corporate security policies. Conventional ACLs work for messenger clients that communicate using specific ports, however, you may find some instant messengers run via a web browser using port 80 for all their message traffic.
Microsoft’s Live messenger (MSN Messenger) is one of them. It is now embedded within the hotmail website. So how do we block web messenger traffic without preventing users from checking their email on the hotmail website?
The answer is using Cisco ASA modular framework policy. The Cisco ASA is capable of inspecting packets at layer 7. This allows us to inspect HTTP packets and help us distinguish the packets we would like to filter.
The Cisco ASA modular policy framework contains 3 components:
– Class map, which identified traffic flows
– Policy map, which associates actions with traffic flows
– The service policy, which activates the policy map
There are two different types of class maps and policy maps. Layer 7 and Layer 3/4. Layer 3/4 is what is used to identify Layer 3/4 traffic using conventional extended ACLs where as Layer 7 class maps (aka inspection class maps) is used to identify application layer traffic patterns specific to the following protocols:
– DNS
– FTP
– IM
– H.323
– HTTP
– SIP
With inspect class maps we are able group multiple criteria and form class map groups to narrow down the specific traffic we are looking for.
Firstly, lets capture the HTTP header information used by the live messenger embedded in the hotmaill page.
In this wireshark image, I have captured a packet used by the live messenger client. By scrolling to the bottom, the HTTP header information is revealed. This is a POST request, with a specific HOST header option destined towards by2msg4010518.by2.gateway.edge.messenger.live.com. This is the string we will be using to filter all traffic leaving the firewall.
After we’ve collected the information, our next step is to create a service policy. Using the ASDM go to configurations > Firewall > Service Policy. Select add a new service policy rule
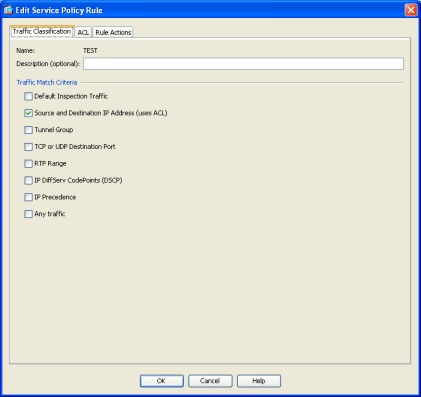
Give the service policy a name. In my setup I have named it TEST. There are several criteria that we will be using to match this traffic, firstly we will use a source and destination ACL to match the match traffic we wish to filter.
Simply select the source and destination IP address (uses ACL) check box.
Next enter the source, destination (any) and service as tcp/http. In my case I’m testing this on a server named WDC01 and selecting “any” and port 80 as my destination since we don’t know and do not care where the live messenger servers are located as long as it is communicating using HTTP.
Next up, we define the rule action. Under Protocol inspection we select HTTP and configure. Select the “Select an HTTP inspect map for fine control over inspection” radio button and click Add.
Click add and give it a name. On the next window select the “details” button. Here we will define the policy action for when we identify a match. In our case, we want to drop the connection and log,
Next select the inspections tab next to the parameters tab and click Add.
We want to select the multiple matches radio button and hit manage.
On the next screen we can define the criteria for identifying the packet we would like to match.
First off lets, define the HTTP POST criteria. Select Add > match type : Match > criterion: request header method > Method: post and hit OK
Next we are going to define the next criteria. We want to match the HTTP header HOST string with anything URL going to messenger.live.com.
Select the criterion: Request Header Field > Predefined: Host > Regular expression click manage
We want to add a Regular expression that catches the string messenger.live.com.
 After select all that. Click OK to the following screens and apply the policy.
After select all that. Click OK to the following screens and apply the policy.
To test, launch your favourite browser and hit login to hotmail. Launch your syslog tool or the real-time log viewer to see the denied packet in action!